How This Tiny AI Model Is Solving the LLM Compliance Crisis
As enterprises race to integrate Large Language Models (LLMs) into their core operations, they are hitting a formidable wall, which is the compliance gap. The friction between the immense utility of cloud-based AI and the strict mandates of data privacy frameworks like GDPR and the EU AI Act has created a dilemma for CISOs and compliance officers. Sending raw customer data or internal intellectual property to a third-party API is often a non-starter for critical infrastructure.
The solution is shifting from a policy-based approach to a technical one: Privacy by Architecture.
The Cloud Leakage Risk
Most LLM integrations rely on sending full prompts to cloud providers. Even with enterprise agreements in place, the transit and processing of Personally Identifiable Information (PII) across network boundaries introduces significant risk. Traditional regex-based scrubbing is often too brittle to handle the nuances of natural language, while deploying massive 70B+ parameter models locally to act as filters is computationally expensive and slow.
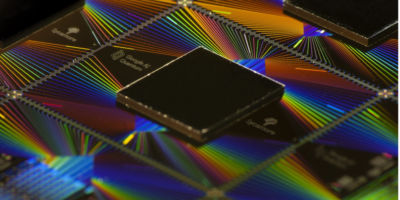
Meet Micro F1 Mask
The Micro F1 Mask, part of the ARPA Micro Series, introduces a high-efficiency alternative. By leveraging a specialized 270M parameter model, which itself is a fine-tune of Google’s Function Gemma 3, it creates a zero-latency privacy firewall that sits between the user and the cloud.
How it Works
The architecture of the F1 Mask is designed to ensure that sensitive data never leaves the local environment. The process follows a three-phase Mask-Vault-Reveal cycle:
-
The Mask (Detection & Tokenization): When a user or agent generates a prompt containing sensitive data (eg. “Draft an email to John Doe at 555-0123”), the F1 Mask intercepts it. The model identifies the entities and outputs a structured
replace_piifunction call. -
The Vault (Secure Mapping) A local middleware bridge processes this function call. The original PII (the name “John Doe” and the phone number) is stored in a local, encrypted Redis vault. These are replaced in the prompt with non-sensitive tokens like
[INDIVIDUAL_1]and[CONTACT_1]. -
The Reveal (Reconstruction) The cloud LLM receives only the sanitized text. It processes the request and returns a response (eg. “Here is the email for [INDIVIDUAL_1]…”). The local middleware then fetches the original values from the Redis vault and reconstructs the final message for the end user.
Why Small Models Win in Security
In the context of critical infrastructure, latency is the enemy of adoption. By utilizing a 270M parameter model, the F1 Mask achieves sub-50ms inference speeds. This allows it to run as a sidecar container in existing Kubernetes pods or even on edge devices without requiring a massive hardware footprint.
Furthermore, the model is highly customizable. ARPA Hellenic Logical Systems released the model with a few ML freebies, and because it is lightweight, organizations can use the included synthetic data generator to create tens of thousands of industry-specific samples, such as specialized medical IDs or proprietary financial codes, and retrain the model locally. This hard-negative mining ensures that the privacy gate evolves as quickly as the threats do.
The Bottom Line
For organizations in regulated industries, the choice is no longer between AI innovation and data security. By implementing a local, high-speed middleware layer for PII scrubbing, enterprises can leverage the power of global cloud LLMs while maintaining absolute data sovereignty.
The Micro F1 Mask demonstrates that effective security doesn’t have to break the bank or slow down the workflow, but it just needs to be built into the architecture.
Technical Resources:
-
Model Weights: arpacorp/micro-f1-mask (Hugging Face)
-
Source Code: arpahls/micro-f1-mask (GitHub)