Cybersecurity is set for a comprehensive overhaul. The US government has finalized a set of standards to make Internet communications secure from attacks by future quantum computers, which could render most current digital protections useless.
The guidelines include one algorithm to enable secure communications through encryption, and two algorithms to protect ‘digital signatures’, which prevent hackers from impersonating a known user or device. They are expected to be adopted on a global scale. The US National Institute of Standards and Technology (NIST) in Gaithersburg, Maryland, selected the three algorithms through a process that began in 2016 and enlisted the help of cryptography specialists worldwide. NIST announced a preliminary selection of four algorithms in 2022, and has now finalized the standards for three of them.
“These finalized standards include instructions for incorporating them into products and encryption systems,” said Dustin Moody, a mathematician at NIST who led the standardization effort, in a statement. “We encourage system administrators to start integrating them into their systems immediately, because full integration will take time.”
“The majority of industry have been waiting for NIST to finalize the standards,” says Bas Westerbaan, a mathematician at the Internet-services company Cloudflare, which is based in San Francisco, California. “It’s great to see that they’re finally out,” adds Peter Schwabe, a cryptographic engineer at the Max Planck Institute for Security and Privacy in Bochum, Germany, who helped to design three of the four systems.
Keeping data secure
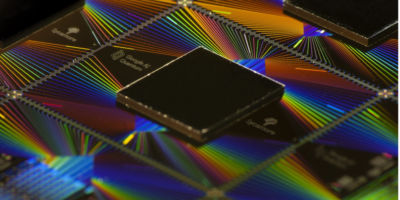
Digital communications and transactions such as online shopping almost universally rely on a small set of algorithms for ‘public-key’ cryptography. These systems allow two parties to exchange information securely. Each party has their own public key, a sequence of numbers that they give to anyone who wants to send them a message. The receiver then can decrypt the message with a private key that only they know.
But current public-key systems are known to be vulnerable to decryption using a quantum algorithm devised by Peter Shor, a mathematician now at the Massachusetts Institute of Technology in Cambridge. In 1994 — when no one had built even the most rudimentary quantum computer and Internet communications were barely starting to go mainstream — Shor showed1 that quantum machines would quickly be able to crack the most popular public-key systems. This could also put devices such as credit cards and security passes at risk of being hacked.
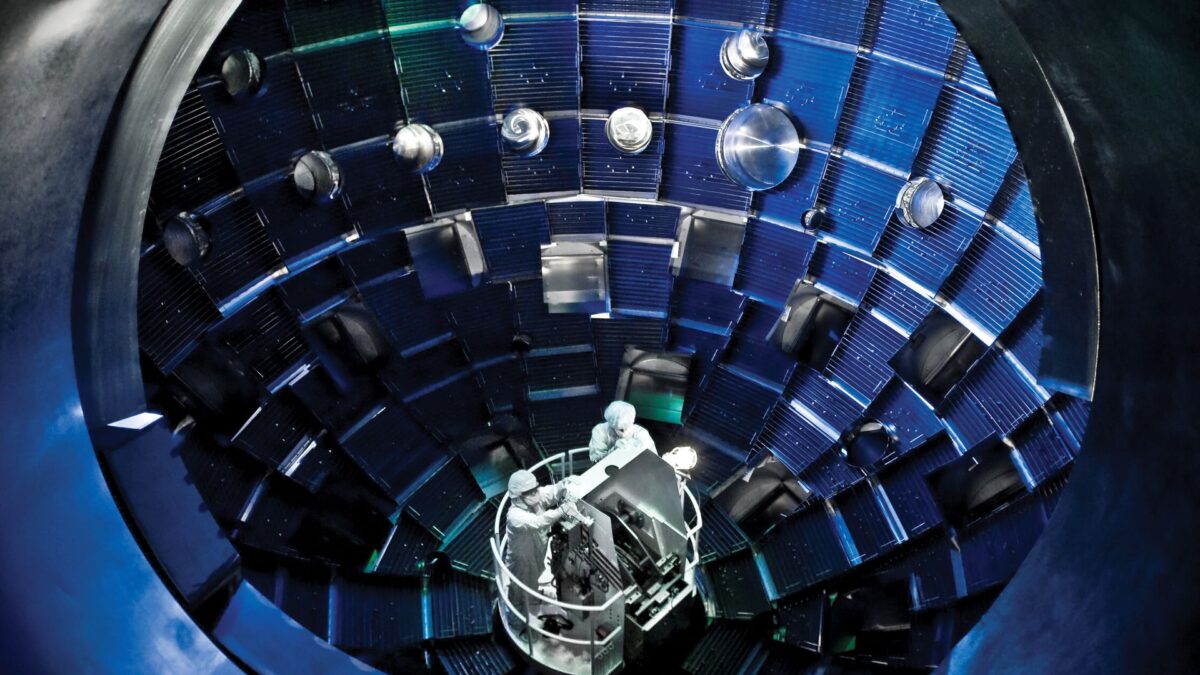
Thirty years later, efforts to build quantum computers have made great progress, but the machines are still said to be at least a decade way from being able to run Shor’s algorithm on anything but numbers with a mere handful of digits. Still, Shor and others have warned against complacency.
The encryption algorithm selected by NIST is called CRYSTALS-Kyber. Schwabe and his collaborators developed it starting from a technique first proposed in 2005 by computer scientist Oded Regev at New York University in New York City. Schwabe says that for the applications most users are familiar with — Internet browsing and smartphone apps — the deployment should proceed relatively smoothly. “Browsers will quickly migrate, as well as messaging apps and video-conferencing systems,” he says. It could take longer for the developers of small Internet- or WiFi-connected devices to catch up, he adds.
Although CRYSTALS-Kyber should be resistant to quantum-computer attacks, no existing public-key algorithms — including the three selected by NIST — has been mathematically proved to be completely safe, and researchers will continue to work on alternatives, just in case. NIST itself is evaluating “two other sets of algorithms that could one day serve as backup standards”, the institute said in a statement.
The NIST announcement made ‘post-quantum’ algorithms official, but they have been available in one form or another for years. Some companies, such as Cloudflare and IBM, have already begun to include them in their systems, but others have been slower to adapt. “Many organizations have not started work on the post-quantum migration at all, citing the lack of standards — a situation that has been called crypto procrastination,” Westerbaan wrote in a blogpost this year. Deploying the encryption algorithm is particularly urgent, he adds now, because “without it, anyone in the future with a quantum computer can decrypt communications captured today”.
doi: https://doi.org/10.1038/d41586-024-02623-y
References
-
Shor, P. W. Proc. 35th Annu. Symp. Found. Comput. Sci. 124–134 (IEEE, 1994).
This article was originally published by Nature.